


In the modern world, medical devices such as pacemakers have become essential for many individuals to maintain a healthy and active lifestyle. These devices are implanted in the body and work to regulate the heart's rhythm, providing a steady flow of electrical pulses to keep it beating at a steady pace. However, as with any technology, these devices are not immune to hacking. In fact, the potential for hacking a pacemaker has become a growing concern in the medical community. Hacking a pacemaker can have dire consequences, including the alteration of the device's settings and even causing the device to stop working altogether. It is essential that manufacturers take the necessary steps to ensure the security and integrity of these devices to protect the well-being of patients.
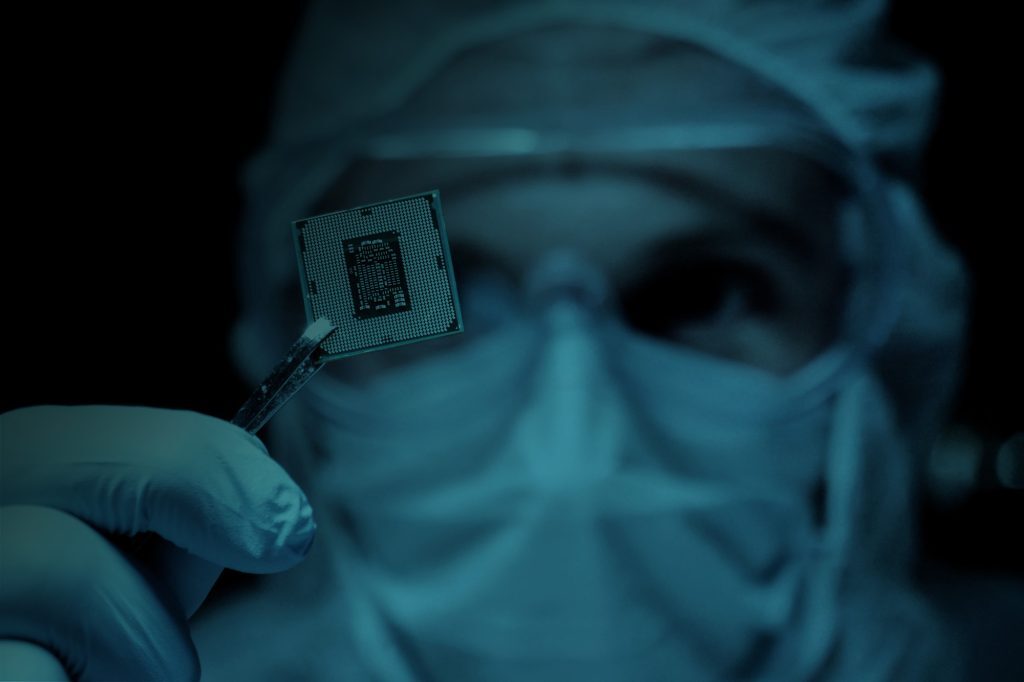
By reverse engineering the firmware, an attacker can identify vulnerabilities, such as bugs or weaknesses in the code, that can be exploited to gain unauthorized access to the device or to steal the personal medical data of the patient. Additionally, this process can also reveal information about the device's functionality and inner workings, which can be used to create malicious firmware that can harm the device and its user – with potentially deadly consequences.
One example of this occurred in 2017, when security researchers discovered that a popular pacemaker was vulnerable to hacking [1, 2, 3, 4]. By reverse engineering the firmware, the researchers were able to uncover a vulnerability that could be exploited to change the pacemaker's settings, such as the heart rate and pacing. This vulnerability could have been used to cause serious harm to the patient, such as inducing a heart attack or even death. The vendor was able to fix the problem by issuing a firmware update, posing additional risk to their patients [1].

Protecting pacemakers against firmware-based attacks is a complex task. One of the main challenges is that pacemakers are embedded systems, which means they have limited processing power and memory. This makes it difficult to implement advanced security features such as encryption or intrusion detection. They often run on older, less secure technology and must maintain high reliability at all times.
Furthermore, pacemakers are critical medical devices that must be highly reliable and available at all times. This means that any security measures implemented must not interfere with the normal functioning of the device or put the patient's health at risk. Manufacturers may lack expertise or resources, face regulatory constraints, and be limited by the cost and development time of adding security features. The US Food and Drug Administration (FDA) is currently working on guidelines for the security of medical devices, recommending the usage of strong cryptographic implementations throughout various layers of the device [5]. However, even if cryptographic measures are implemented, bugs or weaknesses in the implementation could be discovered through reverse engineering, still potentially putting the device and patient at risk. Thus, a combination of technical expertise, regulatory compliance, and an understanding of the unique challenges of embedded medical devices is required to effectively protect pacemakers from firmware-based attacks.

Emproof Nyx can help protect pacemakers from firmware-based attacks by providing a robust and easy-to-use software solution specifically designed for embedded systems. It uses a combination of code obfuscation, tamper detection, and real-time exploitation prevention to protect against a wide range of attacks. The solution is lightweight and low-overhead, making it ideal for use in pacemakers where real-time processing is critical. Additionally, Emproof Nyx does not require access to the source code, which means vendors can protect their valuable IP without giving it away. The solution is also flexible, allowing run-time critical parts of pacemakers to remain untouched, avoiding interruption of critical functions. Overall, Emproof Nyx offers a simple and effective solution for protecting pacemakers and the personal medical data of patients.
The potential for hacking pacemakers through reverse engineering the firmware is a serious concern. Emproof Nyx offers a solution to protect pacemakers against these types of threats by using code obfuscation, tamper detection, and real-time exploitation prevention. These features make it difficult for hackers to find vulnerabilities and exploit them, ensuring the safety and security of the patients using these devices. Emproof Nyx is lightweight, flexible and does not require access to source code, making it an ideal solution for manufacturers to protect their devices and intellectual property.


Our functional safety compliant and trusted solution protects your embedded system.
Contact Us